The 2011 Wiretap Report was released this weekend, providing an overview of how federal and state governments used wiretapping powers in criminal investigations. (Surveillance for intelligence purposes is covered in a separate, far less informative report.) There’s plenty of interesting detail, but here’s the bottom line:
After climbing 34 percent in 2010 the number of federal and state wiretaps reported in 2011 deceased 14 percent. A total of 2,732 wiretaps were reported as authorized in 2011, with 792 authorized by federal judges and 1,940 authorized by state judges.… Compared to the numbers approved during 2010 the number of applications reported as approved by federal judges declined 34 percent in 2011, and the number of applications approved by state judges fell 2 percent. The reduction in wiretaps resulted primarily from a drop in applications for narcotics.
So is the government really spying on us less? Is the drug war cooling off? Well, no, that’s lesson number one: Government surveillance is now almost entirely off the books.
The trouble, as Andy Greenberg of Forbes explains, is that we’ve got analog reporting requirements in a digital age. The courts have to keep a tally of how often they approve traditional intercepts that are primarily used to pick up realtime phone conversationse—96 percent of all wiretap orders. But phone conversations represent an ever-dwindling proportion of modern communication, and police almost never use a traditional wiretap order to pick up digital conversations in realtime. Why would they? Realtime wiretap orders require jumping all sorts of legal hurdles that don’t apply to court orders for stored data, which is more convenient anyway, since it enables investigators to get a whole array of data, often spanning weeks or month, all at once. But nobody is required to compile data on those types of information requests, even though they’re often at least as intrusive as traditional wiretaps.
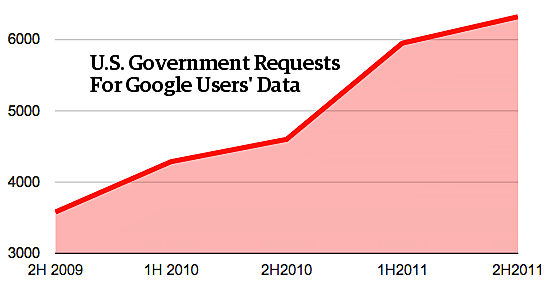
From what information we do have, however, it seems clear that phone taps are small beer compared to other forms of modern surveillance. As Greenberg notes, Verizon reported fielding more than 88,000 requests for data in 2006 alone. These would have ranged from traditional wiretaps, to demands for stored text messages and photos, to “pen registers” revealing a target’s calling patterns, to location tracking orders, to simple requests for a subscriber’s address or billing information. Google, which is virtually unique among major Internet services in voluntarily disclosing this sort of information, fielded 12,271 government requests for data, and complied with 11,412 of them. In other words, just one large company reports far more demands for user information than all the wiretaps issued last year combined. And again, that is without even factoring in the vast amount of intelligence surveillance that occurs each year: the thousands of FISA wiretaps, the tens of thousands of National Security Letters (which Google is forbidden to include in its public count) and the uncountably vast quantities of data vacuumed up by the NSA. At what point does the wiretap report, with its minuscule piece of the larger surveillance picture, just become a ridiculous, irrelevant formality?
Lesson two: The drug war accounts for almost all criminal wiretaps. Wiretaps may be down a bit in 2011, but over the long term they’ve still increased massively. Since 1997, even as communication has migrated from telephone networks to the internet on a mass scale, the annual number of wiretaps has more than doubled. And as this handy chart assembled by security researcher Chris Soghoian shows, our hopeless War on Drugs is driving almost all of it: for fully 85 percent of wiretaps last year, a drug offense was the most serious offense listed on the warrant application—compared with “only” 73 percent of wiretaps in 1997. Little surprise there: when you try to criminalize a transaction between a willing seller and a willing buyer, enforcement tends to require invasions of privacy. Oddly, law enforcement officials tend to gloss over these figures when asking legislators for greater surveillance authority. Perhaps citizens wouldn’t be as enthusiastic about approving these intrusive and expensive spying powers if they realized they were used almost exclusively to catch dope peddlers rather than murderers or kidnappers.
Speaking of dubious claims, lesson three: The encryption apocalypse is not nigh. As those of you who are both extremely nerdy and over 30 may recall, back in the 1990s we had something called the “Crypto Wars.” As far as the U.S. government was concerned, strong encryption technology was essentially a military weapon—not the sort of thing you wanted to allow in private hands, and certainly not something you could allow to be exported around the world. Law enforcement officials (and a few skittish academics) warned of looming anarchy unless the state cracked down hard on so-called “cypherpunks.” The FBI’s Advanced Telephony Unit issued a dire prediction in 1992 that within three years, they’d be unable to decipher 40 percent of the communications they intercepted.
Fortunately, they lost, and strong encryption in private hands has become the indispensable foundation of a thriving digital economy—and a vital shield for dissidents in repressive regimes. Frankly, it would probably have been worth the tradeoff even if the dire predictions had been right. But as computer scientist Matt Blaze observed back when the 2010 wiretap report was released, Ragnarok never quite arrives. The latest numbers show that investigators encountered encryption exactly 12 times in all those thousands of wiretaps. And how many times did that encryption prevent them from accessing the communication in question? Zero. Not once.
Now, to be sure, precisely because police seldom use wiretap orders for e‑mail, that’s also a highly incomplete picture of the cases where investigations run up against encryption walls. But as the FBI once again issues panicked warnings that they’re “going dark” and demands that online companies be requried to compromise security by building surveillance backdoors into their services, it’s worth recalling that we’ve heard this particular wolf cry before. It would have been a disastrous mistake to heed it back then, and on the conspicuously scanty evidence being offered during the encore, it would be crazy to approach these renewed demands with anything less than a metric ton of salt.