At 12:51pm on January 18, 2018–just a day before it was set to expire–the Senate followed the House’s lead and reauthorized the Foreign Intelligence Surveillance Amendments Act (FAA) Section 702 mass surveillance program for another six years by a vote of 65–34.
Writing for JustSecurity.org in October 2017, I made this prediction about the then-looming debate over extending the mass surveillance authority embodied in Section 702:
Absent another Snowden-like revelation, Section 702 of the FAA will be reauthorized largely without change, and any changes will be cosmetic, and almost certainly abused. Whether it has a “sunset” provision or not is now politically and practically meaningless.
As it turns out, that prediction was optimistic. But first, a recap of the events of this week.
The real drama took place Tuesday evening, when Senate Majority Leader Mitch McConnell (R‑KY) held open the procedural vote to end debate on the underlying Section 702 bill, S. 139, by some 90 minutes. The last two holdouts–John Kennedy (R‑LA) and Claire McCaskill (D‑MO) were worked over by anti- and pro-Section 702 forces on the Senate floor, with Senate Intelligence Committee Chairman Richard Burr (R‑NC) calling in reinforcements in the form of Director of National Intelligence Dan Coats to help strong-arm Cassidy and McCaskill into voting to end debate on the bill. The pressure worked, with McCaskill providing the key vote to kill any chance of amending a bill that Senators Ron Wyden (D‑OR) and Rand Paul (R‑KY) declared was a direct threat to the Fourth Amendment rights of Americans.
Speaking after the procedural vote to kill debate on S. 139, Kennedy told reporters, “I was undecided when I walked on the floor, but the program expires Friday, and I don’t want to play with fire. This is an important program.”
Kennedy’s “playing with fire” reference was a clear manifestation of the political fear he felt. After admitting he was undecided, he elected to be swayed by that fear–fear that the program would lapse without his vote. Fear stoked by the presence of DNI Coats, hovering just off of the Senate floor. Fear that if anyone died in a Salafist-initiated domestic terrorist attack in the period of time between the program’s alleged expiration and renewal, he (Kennedy) would be blamed for it. His Missouri colleague, McCaskill, who is up for reelection this year in what will no doubt be a tough fight in a state Trump won in 2016, probably went through exactly the same things in her mind before casting the deciding vote to end debate and move S. 139 forward–with no chance to amend it.
But would the Intelligence Community have have “gone dark” if the Senate had elected to continue debate beyond January 19 and allow amendments to the bill? No.
FISA Court orders issued under Section 702 are generally a year in length, which means that any orders issued prior to the technical legal expiration date would’ve been valid for another 12 months. Additionally, Section 702 is not the only authority under which the National Security Agency (NSA) can collect foreign intelligence information. Executive Order 12333, originally issued during the first Reagan administration, provides sweeping overseas intelligence collection authority that, at present, is not subject to any judicial review.
Indeed, it’s EO 12333 that makes possible programs like RAMPART‑A, as revealed in the Snowden Archive and reported by The Intercept in 2014:
It has already been widely reported that the NSA works closely with eavesdropping agencies in the United Kingdom, Canada, New Zealand, and Australia as part of the so-called Five Eyes surveillance alliance. But the latest Snowden documents show that a number of other countries, described by the NSA as “third-party partners,” are playing an increasingly important role – by secretly allowing the NSA to install surveillance equipment on their fiber-optic cables.
The NSA documents state that under RAMPART‑A, foreign partners “provide access to cables and host U.S. equipment.” This allows the agency to covertly tap into “congestion points around the world” where it says it can intercept the content of phone calls, faxes, e‑mails, internet chats, data from virtual private networks, and calls made using Voice over IP software like Skype.
Not surprisingly, Senator Burr failed to mention these facts during his pitch to his colleagues to renew the Section 702 program on Tuesday or today.
Also on Tuesday, Burr made the following assertions:
Let me just say from the start, this is the single most reviewed program that exists in the Federal Government. This is reviewed congressionally–it is reviewed by the courts, it is reviewed by the DNI, it is reviewed by the inspector general and the Department of Justice–because, on the committee, we realize this requires not just the stamp of approval from Congress but the assurance by the Intelligence Committee and by every branch of government that it lives within the parameters we set.
Let’s examine each of these claims in turn.
Congressional review: Because House and Senate Intelligence Committee proceedings take place in secret, the public has no access to the committee hearing transcripts. We don’t how exacting the questioning is, whether a committee had to employee a subpoena to get documents or witness cooperation, or what independent inquiries–like the Senate Intelligence Committee investigation into the CIA’s torture program–have actually been conducted into Section 702 or any other program. This secrecy is only partly necessary. It should be possible to at least get declassified summaries of the issues and problems involving these programs that have actually been examined in depth without compromising any legitimately classified sources or methods. That we are not is a red flag.
FISA Court review: How effective is the FISA Court in preventing Fourth Amendment violations of Americans rights under the Section 702 program? Not very, as the activist group Demand Progress noted in a report issued in 2017. As the Demand Progress press release stated, “The report identifies overreaches by the Intelligence Community. These include Constitutional problems, unauthorized information collection, failure to comply with FISA Court orders, failure to provide notice to defendants, and mismanagement of acquired data.”
Neither Senator Burr or any other Section 702 supporter referenced these violations during debate over S. 139.
DNI review: The DNI is a program proponent, not an objective overseer. DNI Coats’ presence just off the Senate floor was designed to ensure ultimate passage of the underlying bill. Burr’s assertion here does not pass the “laugh test.”
IG review (including DoJ): The last Section 702 Department of Justice Inspector General compliance report was issued in 2012, and was only declassified in part due to litigation by the New York Times. Thus, the public has no idea whether additional compliance reports have actually been produced, much less what they’ve found. Moreover, recent reporting by investigative journalist Jenna McLaughlin at Foreign Policy raises disturbing questions about the very integrity of Inspector General offices across the Intelligence Community, including the Intelligence Community Inspector General office itself. Not only is Burr not on the letter requesting a Government Accountability Office (GAO) review of the allegations, he made no mention of the controversy during his remarks on Section 702 reauthorization.
The fact that Burr does not appear to be interested in ensuring that IC whistleblowers can come forward to safely report problems with Section 702 or other surveillance programs makes a mockery of his claims that any IG examination of Section 702 can be trusted.
I began this piece by noting that my prediction last October that Section 702 would be reauthorized with minimal or cosmetic changes had proved optimistic. The Brennan Center’s description of the actual effects of S. 139 tell the tale:
When Congress reauthorizes Section 702 of FISA—a law intended to authorize surveillance of foreigners only—it should take the opportunity to shore up privacy protections for Americans. S. 139 does the opposite. It codifies the government’s practice of “backdoor searches” without any meaningful restriction. It also authorizes an expanded form of “abouts” collection. It thus leaves Americans’ privacy more vulnerable, not less.
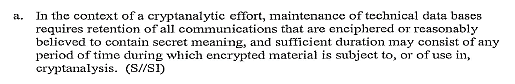
Burr and other Section 702 reauthorization proponents have also asserted that the program does not deliberately target Americans–that any communications of Americans swept up in Section 702 dragnet are “incidentally” collected. But there’s nothing “incidental” about deliberately targeting people–including Americans at home or abroad–who use the Tor anonymity tool for online browsing–something NSA has been doing for at least a decade. And as the Section 702 “minimization” procedures approved by then-Attorney General Eric Holder in 2009 make clear, NSA can keep and analyze any domestic U.S. communications acquired that employ any form of encryption:
With the growing number of Americans utilizing apps like Signal, Wickr, and similar encrypted messaging apps, it means the total number of Americans NSA can target for simply using encryption to protect their privacy will grow.
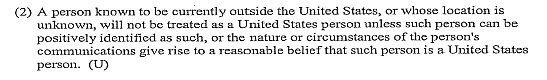
And if NSA can’t figure out for sure if you are, in fact, a U.S. citizen, they will target you until they can prove otherwise:
The bill the Senate just passed and that President Trump will sign makes all of these problems worse. It’s another tragic example of the triumph of fear over liberty in the Digital Age.